Illicit use of Alternative Currencies
Written By: CENSA Editorial Board
—
A recent Treasury Department study entitled “The National Terrorist Financing Risk Assessment”[1] briefly discussed emerging methods in the world of terrorist and criminal financing that may soon become “threats.” The use of digital, or alternative, currencies was included on the list of new and emerging capabilities. And although the report remained inconclusive on whether or not terrorist groups such as the Islamic State (IS) have begun using such methods, one should look no further than the findings being reported in the aftermath of the Paris attacks that this is likely the case.[2] Since early 2013 the risk is great and should be given more attention.
Alternative currency and alternative payment systems are in fact electronic cryptocurrencies used to purchase both virtual and actual goods and services. Sometimes called “virtual currency,” these transactional methods are not secured with or backed by physical assets or protected by any legal currency laws—by any nation state or global entity—and nor are they in fact controlled or even regulated by any central governing authority outside of the communities themselves. Since the establishment of Bitcoin in 2009, literally hundreds of cryptocurrencies[3] have become available for facilitating trade and other transactions in online markets. And over the past several years these alternative currencies have grown in popularity and are traded in their own right and in their own markets, much like stock (as shown below in Figure 1).[4] Given the rise in the number of online options, anyone with a connection to the Internet can buy, sell, and trade in virtual commodities.

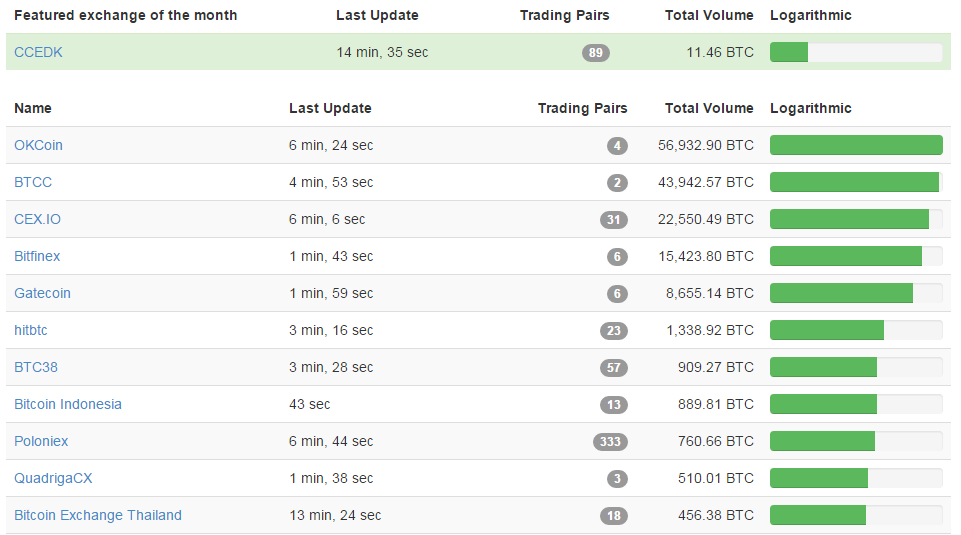
Figure 1 – Example of Cryptocurrency Markets
More recently, indeed over the past few months, independent anti-terrorism hacker collectives, contributors to “deep web” forums, and other digital media sources, have been working to identify and track the illicit use of alternative currencies. Interest in the origins of IS’s financial strength has increased given the rise in violence directly tied to or inspired by the group. Ghost Security Group (GhostSec) has attempted to identify and publicly call-out IS’s use of alternative currencies and has specifically focused on Bitcoin.[5] While both GhostSec and the Treasury Department[6] largely believes that the majority of IS funding derives from black market oil sales and various acts of extortion, some evidence suggests that a portion of IS financial strength is now stored and traded in digital currencies. As for IS funding originating in alternative currency via cryptocurrency mining, however, the current amount is likely small.
For both terrorists and criminals, a degree of anonymity is one of the main attractions of alternative currencies for the illicit marketplaces of the ether. The widespread use of the SHA-256 protocol, a cryptographic hash function, and the use of a digital wallet system, like the bitcoin block chain ledger (described fully here), together provide an effective level of managed-attribution for a user. The IS, with its self-proclaimed global mission and worldwide base of support, has a vested interest in the use of such online options as a means for coordinating and maintaining its current level of operations. IS is therefore likely using alternative currencies the following ways:
- As a Call to the Cause: Funding, Recruitment, Propaganda. These are the activities that allow IS to operate and grow and must be maintained through a global support network capable of timely engagement with recruits from afar. One tactic that has been effectively employed is the simultaneous use of digital wallets for donation purposes in conjunction with targeted propaganda techniques aimed at convincing others it is their duty to support the group, if not physically then monetarily, with however small a donation. Earlier this year a teenager based in Manassas, Virginia, was sentenced to 136 months in prison after pleading guilty to providing both resources and material support and for offering online advice about how to use Bitcoin to fund the IS.[7]
- For the purchase, sale, and trade of illicit goods in “Dark Markets”: The dark web hosts online markets with everything from drugs to small heavy weapons to stolen credit cards. All such trade is performed with alternative currencies, usually Bitcoin, and offers a fertile ground for the Islamic State to not only conceal its purchases of needed goods but could also facilitate the sale of war spoils.
- For the payments and services: In a blog that has since been removed from the Internet[8], IS posted notices about the use of alternative currencies for avoiding detection and then highlighted the consequential benefits of enabling tax evasion. Furthermore, the blog promoted alternative currencies as allowing distant supporters to receive stipends and other payments.
And yet at some point in the alternative currency process a level of vulnerability is present because some amount of attribution must always exist and can be exploited by analysts. While Bitcoin remains digital, for example, it has limited use, impact, and value in the marketplace until it is traded for and converted into a tangible currency, or transactional service or good. This point of conversion is a vulnerability; and with a finite amount of hard currency in IS-controlled areas available for “cashing out,” IS will need to rely on the global network in places throughout Europe, Canada, and the United States. At a minimum, the monitoring of such conversions can be utilized for gathering information about the group’s overall activity.
Ultimately, the digital ubiquity that is constant within the modern battlefield, combined with the growing technological challenges for security (encryption and inexpensive protocols) will demand that our national security professionals, in some sense, resort back to the days of good old detective work – but in the digital domain – to discover these points of vulnerability. An effective defense therefore will demand a passive, yet aggressive, offense. We need to get on with it.

[1] https://www.treasury.gov/resource-center/terrorist-illicit-finance/Documents/National%20Terrorist%20Financing%20Risk%20Assessment%20%E2%80%93%2006-12-2015.pdf
[2] http://www.ibtimes.co.uk/paris-attacks-eu-crack-down-bitcoin-transfers-attempt-strangle-isis-funding-1529693, http://anonhq.com/anonymous-reveals-isis-militants-linked-to-paris-attack-had-bitcoin-funding/
[3] http://www.cryptocoincharts.info/coins/info, http://coinmarketcap.com/
[4] http://www.cryptocoincharts.info/markets/info
[5] http://www.networkworld.com/article/3005308/security/hacktivists-claim-isis-terrorists-linked-to-paris-attacks-had-bitcoin-funding.html
[6] https://www.treasury.gov/press-center/press-releases/Pages/jl9755.aspx
[7] http://insidebitcoins.com/news/american-teen-sentenced-to-11-years-for-helping-isis-with-bitcoin/34576
[8] https://alkhilafaharidat.wordpress.com/ [Please use caution when opening this link]

